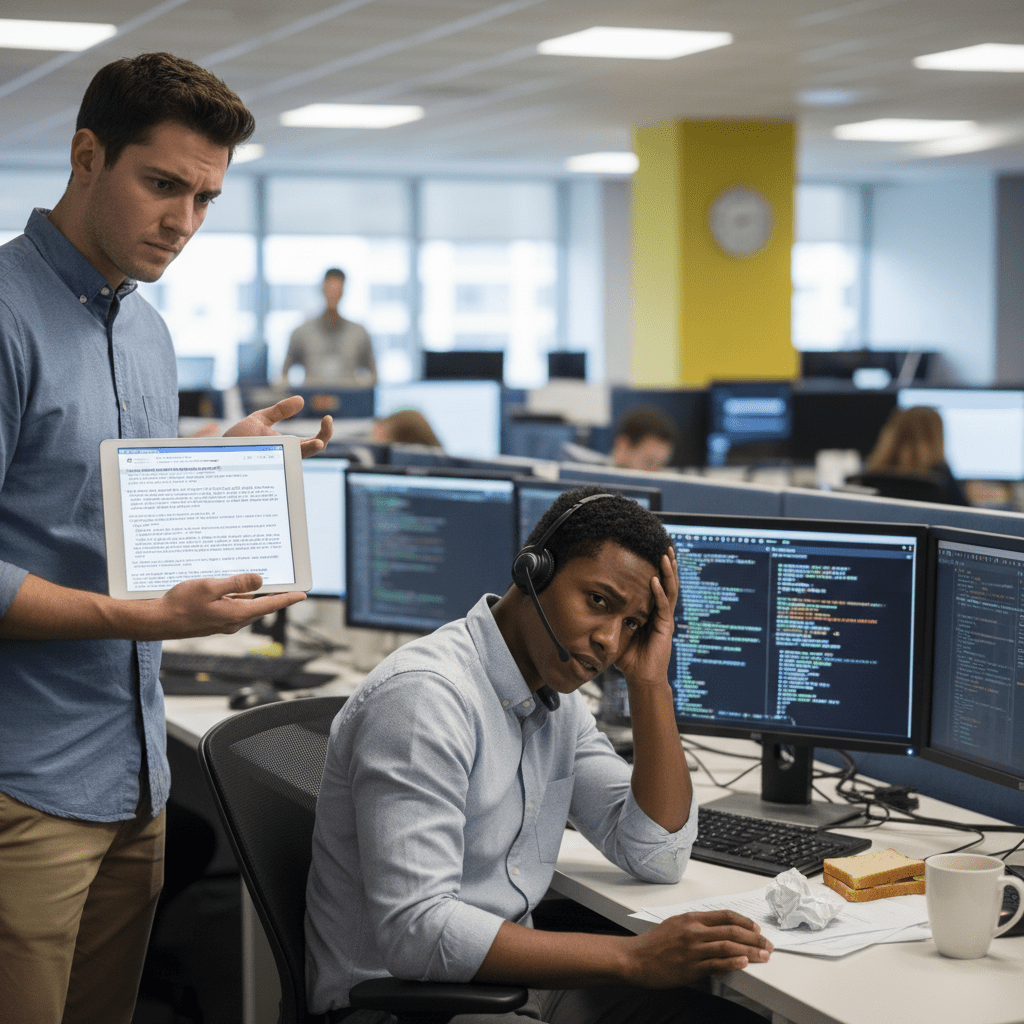
It started, as most things do, with a simple, desperate need. I was in a group chat, trying to convey a very specific state of being: the feeling when you’ve just pushed code to production and the bug reports haven’t started… yet. It’s not full-blown terror, not yet. It’s a low-grade, simmering anxiety, masked by a thin veneer of professionalism. We needed an emoji for this. I called it “Mildly Panicked But Holding It Together.” Genius, right? The world would thank me. All I had to do was submit it.
The Submission Portal to Another Dimension
I naively assumed there was a website with a big friendly button that said, “Got a Cool Emoji Idea? Click Here!” Instead, I found the Unicode Consortium. This isn’t a company; it’s a global standards body that sounds like it was named in a sci-fi B-movie. Their emoji submission process involves a PDF document that is, I kid you not, longer than the instruction manual for a mid-sized commercial aircraft. You don’t just ‘suggest’ an emoji. You file a formal proposal, complete with evidence, justifications, and frequency-of-use charts for a thing that does not yet exist.
The Evidence I Was Required to Gather
My simple, relatable idea had to be defended like a doctoral thesis. The requirements were staggering:
- Evidence of Widespread Use: I had to prove people were already trying to convey this emotion using inferior emoji combinations, like the grimacing face plus the sweat droplets. I spent a week taking screenshots of Slack channels like an anthropologist studying a lost tribe.
- Distinctiveness: I had to write a multi-page essay arguing why my “Mildly Panicked” emoji would not be confused with “Slightly Concerned,” “Worried,” or “Anxious Smile.” The semantic nuances were debated with the seriousness of a UN resolution.
- Vector Graphics: I had to provide my own artwork in black & white and full color, in specific file formats, proving my emoji could be rendered at 72×72 pixels. I don’t draw. I write scripts. My first attempt looked like a jaundiced potato.
After weeks of work, I submitted my proposal and it vanished into the digital ether. Months later, I received a one-line email: “Proposal CLDR-47b-1138 is now under review by the Subcommittee for Emoji Ad-Hoc Review.” There’s a subcommittee. Of course there is. I imagine a group of very serious people in a windowless room, sipping room-temperature water and debating the cultural implications of my panicked little yellow circle. The emoji still hasn’t been approved, but I’ve learned a valuable lesson: behind every simple, delightful icon on your phone is a bureaucratic labyrinth so vast and complex, it would make a government agency blush.